During past few months I’ve witnessed and been targeted by rather simple, but still interesting phishing campaign. Well, not me personally, but instead a YouTube channel that I run. This campaign has noticeably sped up in November, so I decided to take a closer look at these phishing emails and share with you my findings.
#1 Despite being hilariously obvious, first four of these were not caught by ProtonMail’s spam filter
I reported these four first ones in the webservice and on Twitter to ProtonMail. The first one I sent to CERT-FI as well. It took few months for ProtonMail’s filters to start recognizing them, but the good news is that now the last five examples, despite having slight variance in them, have been caught automatically. But just look at these first two that I got, hopefully no one fell for these:


#2 Out of several YouTube channels I manage, only one has been targeted
This targeted channel was not the biggest or most successful in any metric. However, it’s the only one that’s monetized. Correlation doesn’t imply causation, but that’s the only reason that makes any sense. After all, these criminals are doing this for money.
Unfortunately, this hypothesis doesn’t seem to hold water when looking at who else have been hit with this phishing campaign. That leads us to finding number 3.
#3 Same email was CC’d to others
Curiously, one of the emails was also sent to two other channel owners. I double checked both of their email addresses from their channels’ About pages. Analyzing their channels, both were smaller than my targeted one, and only one of them was monetized. So, there goes that theory. I contacted and warned both of these channels on Twitter, but they didn’t respond.
After that email, all later ones have been sent to youtube(a)control.com and the real recipient(s) have been BCC’d. Control dot com is seemingly unrelated site, at least it appears to host a legitimate forum. I’m not an expert in this matter, but I’d assume all of that is easy to populate / fake. This new forum was launched very recently, November 12, and the domain itself has been updated in September with GoDaddy. Control’s YouTube channel has been created October 31, but it doesn’t have any content or other details. Again, all of this might be irrelevant. “Control” has popped up couple of times in the sender addresses too, tough.
#4 Unclear where they have found my email address
I guess a non-finding is a finding as well in this case. That email address is used nowhere else and nothing comes up with it from search engines. I also ran the email address and short version of it through breach databases, but I didn’t get any hits.
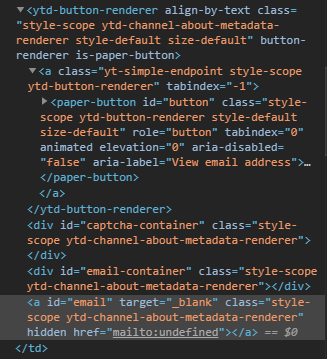
YouTube channel email addresses are publicly available on channels’ About pages, but they are hidden behind a button element and usually CAPTCHA, too. Bypassing Google’s CAPTCHA can be done, but all in all this kind of scraping seems like a massive effort compared to the possible gains. I guess with good enough automation these kind of campaigns become plausible.
#5 Senders’ email service providers started as Russian. Little to no typosquatting involved.
In the order of oldest to newest,
From – Address – Provider:
- YT Support – yt-controler – mail.ru
- YT Support – ytube-sup – mail.ru
- YouTube – drudinconsie3 – mail.ru
- YouTube – gulyaevvyacheslavmoy – inbox.ru
- YouTube Support – youtube.control.4 – zohomail.eu
- YT Support – nikiforovaolesyadbp – inbox.ru
- YouTube – youtube.4 – zohomail.eu
- YouTube – youtube.0 – zohomail.eu
- YouTube – youtuber.support – zohomail.eu
For reference, these are the legitimate addresses that contact YouTube channel owners:
- Google – no-reply – google.com
- YouTube – no-reply – youtube.com
- YouTube Creators – no-reply – youtube.com
#6 After few iterations, phishing content seems to have reached its final form (for now)
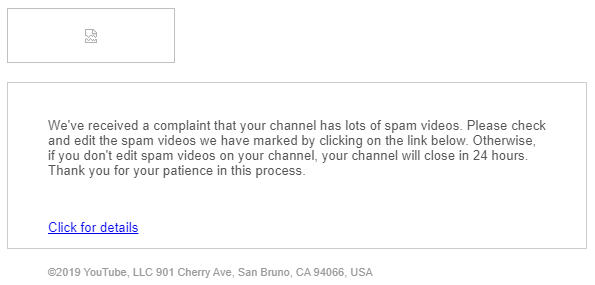
Although the copy, design and message have changed a bit during the campaign, they still rely on the two classics: fear (“comply or channel will be deleted”) and hurry (“do this in 24 hours”). Message sizes have been varying from 536 B to 22 KB, the largest ones being three which included images. Rest of them have remote content, but I haven’t downloaded those either.
Sending times have been between and 6:16 PM and 8:00 AM UTC+2.
The CTA links all point to different short URLs, none of which is even remotely related to YouTube or Google. As these links tend to be short-lived, I’m not surprised to see them vary between emails. One interesting URL to highlight is this one from earlier this month: tiny dot cc/ytcontoller This one again falls into the same “controller” category as discussed earlier. This was also the email that was sent to those two other channels.
This is how the final form looks like, and it has been like this in the past three emails:
This article is obviously not a serious investigation of this phishing campaign. I consider this more as a PSA for fellow YouTubers. I’ll come back to this topic if anything radical happens with this campaign.
One thought on ““YouTube channel will be disabled within 24 hours!” Phishing Campaign First Look”